We’re working through functions in my college-prep pre-calculus class; meaning a more rigorous treatment of domain, range, and composition ideas than what students experienced in earlier courses. As I was about to start inverses last week, I sought an activity which would provide some discovery, some personalization, and less of me rambling on.
These are the times when searching the MTBoS (math-twitter-blog o’sphere) leads to some exciting leads, and the search for inverse functions ideas didn’t disappoint – leading me to Sam Shah’s blog, and an awesome discussion of inverse functions which I turned into a sharing activity. A great list of blogs and MTBoS folks appears on this Weebly site.
To start, I wrote a function on the board, and asked students to think about the sequence of steps needed to evaluate the function:
The class was easily able to generate, and agree upon a list of steps:
- Square the input
- Multiply by three
- Add 1
From here, I asked the class to divide into teams of 2. Each partnership was then given two functions on printed slips (shown below) to examine: list the steps of the function, and provide 3 ordered pairs which satisfy the function.
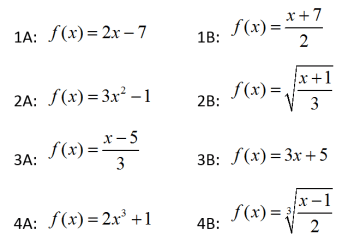
THE FUNCTIONS:
Notice that the functions are arranged so that A and B in each set are inverses. Partners were given two different functions, but never an inverse pair. So a team could get 2A and 4B, but not 3A and 3B.
My plan was to complete this entire activity in one class period, BUT weather took hold. They day we started we had a two-hour delay, and the next two days were lost due to snow, then a weekend. SO, the best-laid intentions of activity, sharing and resolution became activity…..then 5 days later.
As we started the next class day, I asked students to review their given functions (and re-familiarize themselves), then seek out the teams who had the other half of the function pair and share information. So a team which had 2B sought out 2A, and so on.
After the sharing, a classwide discussion of the pairs was then seamless. Students clearly saw the relationships beteen the inverse pairs and the idea of “undoing” steps, and we could now apply formal definitions and procedures with an enhanced understanding. Also, by sharing ordered pairs, students saw the domain-range relationship between functions and their inverses, and this made graphing tasks much easier. I’m definitely doing this again!
Finally, notice that pair 2A / 2B features a quadratic / square root. While we didn’t dive right in at the time, this set the trap for a discussion of one-to-one fucntions and the horizontal line test the next day.